Claude Code source code leaked: a security shock and the immediate to-do list for enterprises
- Apr 1
- 3 min read
The incident on March 31, 2026, where the Claude Code source code (approximately 9.8 MB in size) was leaked, is not just Anthropic's problem. It is a red alert for Supply Chain Security.
When the source code of a CLI (Command Line Interface) tool with deep file system privileges is exposed, every organization using it faces the immediate risk of internal attacks.
1. Analyzing the root cause: From "mythos" to the 9.8 mb source code leak blunder
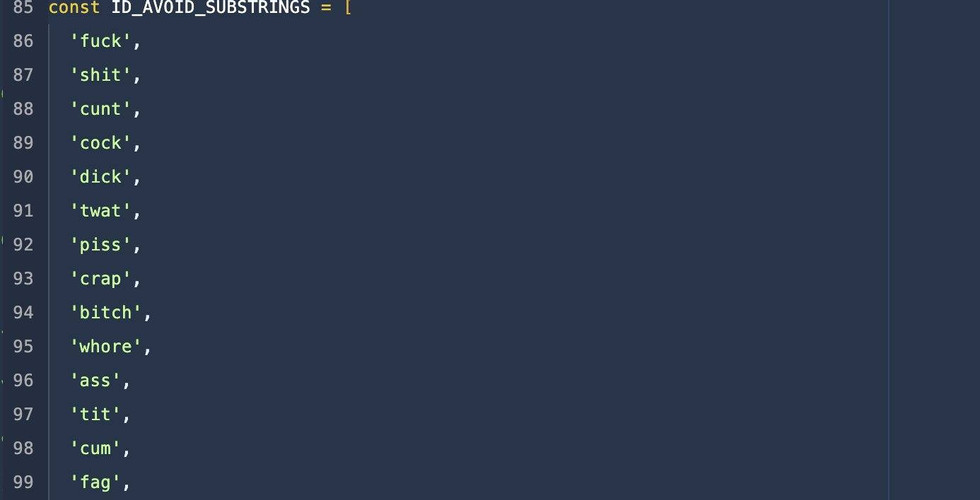
This leak is not merely an exposure of logical code lines. Reports from VentureBeat and CNBC indicate that this source code contains internal API interaction methods and potentially Hardcoded Credentials.

Experts define this flaw as a combination of Broken Access Control and Insecure Project Management. The fact that Anthropic exposed the "Mythos" project just days prior proves that their CI/CD pipeline is suffering from severe vulnerabilities regarding the separation of testing and production environments.
2. Solutions: Emergency actions enterprises must take immediately
If your enterprise or development team is using Claude Code, execute the following steps immediately to cut off potential attack vectors:
Step 1: Temporarily Suspend & Revoke Access: Disconnect Claude Code from the company's source code repositories (GitHub, GitLab, Bitbucket). Revoke all Personal Access Tokens (PATs) or OAuth Tokens granted to this tool.
Step 2: Rotate API Keys: Immediately rotate all API Keys related to Anthropic, AWS, or any cloud services that Claude Code has access to. Attackers could extract the "fingerprints" of these tokens from the leaked source code to execute spoofing attacks.
Step 3: Local Environment Cleanup: Inspect .env files, .bash_history, or temporary storage files on employee workstations to ensure no sensitive data was "accidentally" collected by Claude Code and pushed to Anthropic's servers during the leak period.
Step 4: Audit System Access Logs: Use monitoring tools (SIEM) to review any anomalous queries from User-Agents related to Claude Code over the past 72 hours.
Reference Note: Based on hands-on field experience, 90% of intrusions following a source code leak stem from an enterprise's delay in Rotating Credentials.
3. Risk assessment from a cybersecurity expert's perspective
The dissemination of this 9.8 MB source code across forums like X and Vietnamese tech news sites like VnReview turns this tool into prime bait for Reverse Engineering attacks.
Some information was leaked from the attack.
Hackers can:
Inject malicious code (Backdoors) into fake distributions of Claude Code.
Exploit Remote Code Execution (RCE) vulnerabilities based on the newly exposed file-handling logic.
In Vietnam, where the usage rate of cracked software and free support tools is notably high, this risk is multiplied exponentially. Enterprises must be extremely vigilant against any unofficial installation packages claiming to be from Anthropic.
4. Strengthening your defense layers with ipsip vietnam
In a landscape where AI Search tools like Google SGE and GEO increasingly prioritize highly authoritative content, maintaining transparency in your security processes is the best way to retain customer trust.
To protect digital assets against similar incidents, enterprises should strongly consider:
Deploying a 24/7 Security Operations Center (SOC) to detect early signs of data leakage.
Conducting periodic vulnerability assessments (Penetration Testing) across the entire internal software development lifecycle.
References:
VnReview: The truth about the Claude Code source code being only 9.8 MB
VentureBeat: Claude Code source code appears to have leaked
Fortune: Anthropic's second security lapse in days - March 2026
CNBC: Anthropic leak internal source code analysis


















Comments