A 3-step strategy for SOCs to neutralize Multi-OS attacks
- Apr 14
- 3 min read
In today’s enterprise environment, employees no longer rely on a single operating system. An organization may simultaneously operate Windows PCs for office staff, MacBooks for executives, Linux infrastructure for technical teams, and a plethora of personal mobile devices. This diversity creates a "fertile ground" for cross-platform attacks.
When attackers can easily move between operating systems, Security Operations Centers (SOCs) often find themselves in a reactive position due to fragmented response processes. This article explores these challenges and how to optimize defense workflows through three core steps.
Why are Multi-OS attacks a "nightmare" for SOC Teams?
Typically, each operating system has its own set of monitoring tools and response procedures. Attackers exploit these gaps to execute intrusion campaigns that span multiple platforms. In such cases, SOC teams face several hurdles:
Delayed verification: Switching between disparate tools increases the time required to assess the severity of an incident.
Limited visibility: It is difficult to gain a holistic view of an attack in its early stages when data is siloed.
Staff overload: Incidents that are not fully resolved at the source lead to escalations, putting immense pressure on high-level specialists.
Consequently, attackers gain "golden time" to steal credentials, establish persistence with malware, or penetrate deeper into core systems.
A 3-step workflow to mitigate cross-platform risks
To stay ahead, leading SOC teams are adopting consistent, end-to-end response workflows. Here are three practical steps to counter these threats:
Step 1: Integrate cross-platform analysis into initial triage
A common mistake is assuming that a specific type of malware will behave identically across all operating systems. In reality, a malicious file on Windows may exhibit entirely different behaviors and risk levels when executed on macOS.
Specifically, macOS is often perceived as "safer" and is sometimes overlooked during monitoring. However, it remains a high-value target as it is frequently used by executives and developers.
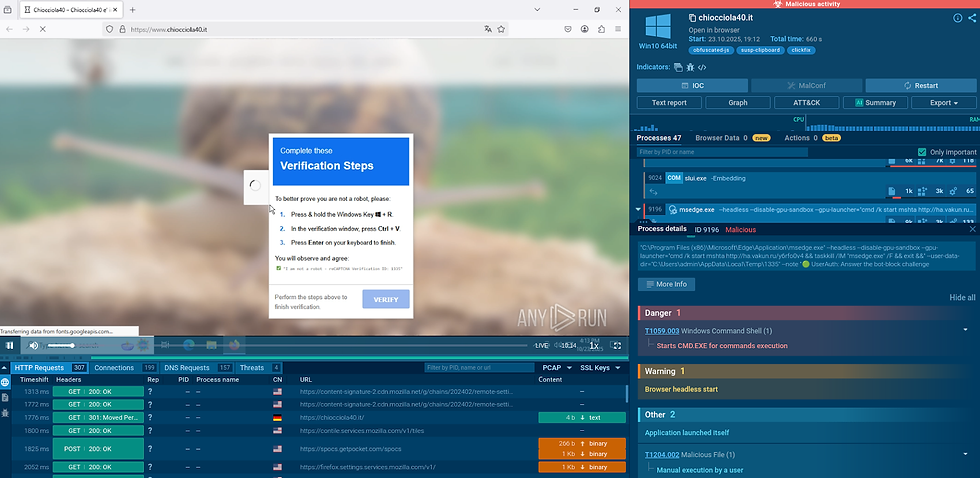
Real-world example from the "ClickFix" campaign: Attackers used fraudulent advertisements to trick users into installing a source code support tool. Depending on the user's OS, different instructions were provided. On macOS, they manipulated users into executing Terminal commands to install "AMOS Stealer" malware, designed to exfiltrate browser data, passwords, and sensitive files.

If the SOC performs cross-platform analysis from the outset, they can quickly identify how attack methods adapt to each OS and implement timely prevention measures.
Step 2: Maintain a unified, centralized investigation process
Instead of splitting an incident into separate mini-investigations for Windows, Linux, or macOS, SOC teams should consolidate everything into a single, unified workflow.
Fragmenting an investigation only leads to data silos and slows down the response time. A unified process helps:
Reduce redundant tasks and simplify evidence management.
Enable analysts to track the attacker’s entire lateral movement path.
Ensure that response actions are synchronized across all environments.
Step 3: Transform visibility into rapid action
Merely observing attacker activity is insufficient; understanding and neutralizing them quickly is what matters. In Multi-OS attacks, data often resembles scattered puzzle pieces.
SOCs need supporting tools to "solve the puzzle" automatically through:
Automated summary reports that clearly display Indicators of Compromise (IOCs).
Leveraging Artificial Intelligence (AI) to assist in complex behavioral analysis.
Visual information presentation so operators can make immediate mitigation decisions instead of wasting time on manual data synthesis.

Measurable results from process optimization
Standardizing cross-platform response workflows not only secures the system but also delivers significant operational efficiency:
Increased productivity: SOC team productivity can increase up to threefold.
Faster response times: Reduces Mean Time to Remediate (MTTR) by an average of 21 minutes per incident.
Reduced personnel pressure: Decreases the workload for Tier 1 analysts by 20% and reduces escalations by 30%.
Improved morale: 94% of users report that incident assessment has become faster and easier, helping to mitigate "alert fatigue."
In the race against cybercriminals, time is the decisive factor. Multi-OS attacks succeed only when our responses are slow and disconnected. By unifying processes and optimizing visibility, enterprises can proactively mitigate critical risks before they cause actual damage.
Reference: The Hacker News










Comments