SOC and MDR: Navigating the differences to choose the optimal defense model
- 11 hours ago
- 5 min read
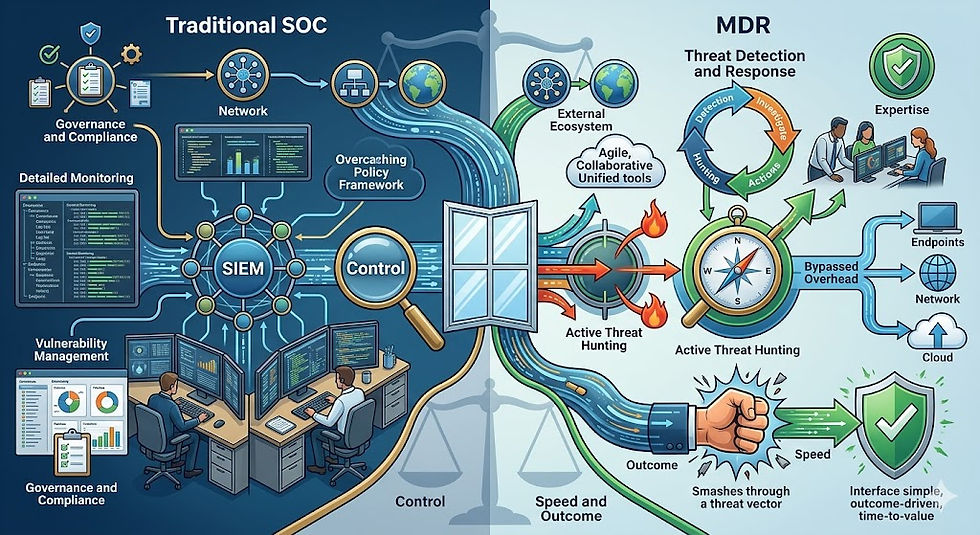
A Security Operations Center (SOC) is an internal department that comprehensively operates all security processes, requiring a massive capital investment. In contrast, Managed Detection and Response (MDR) is an outsourced security service that focuses specifically on response speed with a cost-effective approach.
Globally, organizations are facing a critical shortage of approximately 4 million cybersecurity professionals, leading to 90% of businesses experiencing data breaches. More alarmingly, the latest reports indicate that the average cost to remediate a data breach has reached $4.88 million.
This severe devastation is forcing management levels to immediately construct protective barriers. However, facing a barrage of dry technical terms like SOC or MDR leaves many leaders confused. This article will dissect these defense platforms in the most accessible way, helping non-experts make accurate investment decisions.
What is a security operations center (SOC)?
For those newly exploring the field, the term SOC (Security Operations Center) is often mistaken for a type of software or a device plugged into a computer. In reality, a SOC is a "nerve center" ecosystem that closely integrates three core elements: People, Technology, and Processes.

To visualize this, imagine a SOC system as the Central Police Headquarters of a major city. This headquarters is not only responsible for catching criminals but also handles a mountain of complex administrative work: monitoring traffic cameras, conducting periodic patrols, reviewing the security vulnerabilities of every house, and ensuring all citizens comply with the law.
For a SOC "Headquarters" to function, a business must prepare three major resources:
Technology investment: Purchasing massive data collection monitoring software (such as SIEM) and internal network scanning systems.
Human resource recruitment: Building an internal team including analysts for continuous monitoring, system maintenance engineers, and threat hunters.
Operational processes: Complying with strict data security laws (such as GDPR or PCI DSS) and establishing response playbooks for every attack scenario.
How does managed detection and response (MDR) operate?
In complete contrast to building an internal center, Managed Detection and Response (MDR) is a 100% outsourced security service. Instead of spending billions to build a Police Headquarters, buy cameras, and hire guards, a business signs a contract with a professional security organization to protect its server systems.
If a SOC is a Headquarters handling all administrative procedures, then MDR is exactly like a Special Weapons and Tactics (SWAT) team. This tactical unit does not concern itself with paperwork or compliance reports; they focus intensely on a single objective: using advanced radar and artificial intelligence (AI) to hunt, surround, and neutralize dangerous malware the moment it appears.
The greatest advantage of MDR is its efficiency. MDR service providers already possess the technological weaponry and elite expert teams. They simply connect their security systems to the customer's environment and immediately activate a 24/7 continuous monitoring network.
Three most recognizable differences between SOC and MDR
To clearly define the boundaries for non-technical individuals, the differences between these two models lie in three vital factors:
Operational responsibility (Who does the work?): With the SOC model, the business must purchase tools, perform installations, and internal IT staff must manually handle alerts. With MDR, the service provider handles everything from tools to experts, directly intervening to lock down hackers without the business needing to perform manual operations.
Scope of protection (What tasks are performed?): A SOC provides a panoramic view, from checking software vulnerabilities and managing identity and access to establishing long-term compliance reports. Conversely, MDR narrows the scope, focusing maximum resources on early incident detection and neutralizing actual threats to prevent system downtime.
Cost and HR risks (How much does it cost?): This is the biggest hurdle. Building an internal SOC requires an extremely large initial capital expenditure (CAPEX). More distressingly, businesses often live in fear of skilled engineers jumping to other companies. Meanwhile, MDR transforms costs into a subscription-based operating expense (OPEX) similar to a utility bill; customers only pay based on usage scale, completely eliminating the burden of recruitment.
When should a business build an internal SOC and when should it hire MDR?
No single solution is absolutely perfect for everyone; the choice depends entirely on the budget and business characteristics:
Businesses should build a SOC when: The organization is a large corporation, a government agency, or a bank with a complex network structure. These entities have substantial budgets and are bound by strict legal regulations requiring full control over sensitive data within their internal systems.
Businesses should hire MDR when: The organization is a small or medium-sized enterprise (SME) with a tight budget that cannot (or does not want to) recruit cybersecurity experts. MDR allows them to immediately possess a high-tier defense system without waiting for long procurement and installation periods.
Hybrid trend: In reality, even giant corporations with internal SOC forces still hire additional MDR services. They use their SOC for daytime operations and hire external MDR teams to guard the system at night, on weekends, or during holidays. This combination prevents internal personnel from being exhausted by thousands of daily false positives.
Why white-label SOC solutions are a "lifesaver" for IT agencies
In addition to regular businesses, technology service providers (such as IT agencies or vendors) also aspire to offer security services to their clients. However, building an internal monitoring infrastructure is a massive barrier, often costing between 1 to 2 billion VND for the initial setup alone.
This is where a White-Label SOC solution emerges as a perfect hybrid model.
Instead of building a machine from scratch, IT partners can leverage the entire infrastructure and 24/7 monitoring services from an original provider, then package and resell it to end customers under their own brand name. This specialized solution helps technology companies scale their business instantly and increase profits without bearing expensive system maintenance costs or worrying about personnel shortages during night shifts.
Why businesses should choose solutions from IPSIP Vietnam
Building a security system from scratch is never a simple story for any organization. Positioning itself as a "strategic partner" with a deep understanding of the pain points in resource and financial management, the IPSIP Vietnam ecosystem provides a comprehensive answer to the technical expertise shortage.

Originating with over 15 years of experience (from France), IPSIP's operation and management systems have successfully passed rigorous audits to achieve international security standards such as ISO 27001:2022 and SOC 2 Type II.
By providing non-stop 24/7 monitoring services—from the Security Operations Center (SOC) and Network Operations Center (NOC) to the IT Support team—IPSIP is ready to establish the strongest defense grid for organizations. Customers directly gain high-level malware interception capabilities without having to maintain a bulky internal workforce.











Comments